The Rise of Collaborative Robots: Transforming Industries
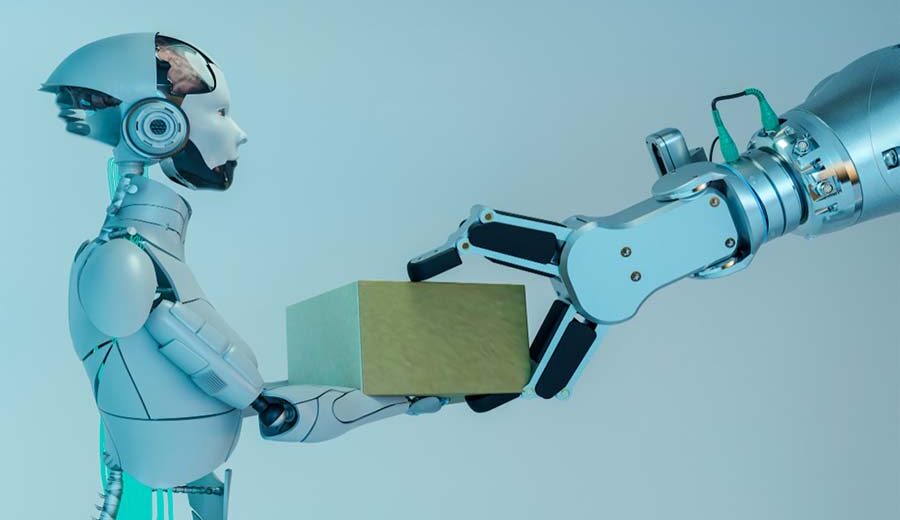
Robots have traditionally been associated with heavy machinery, assembly lines, and manufacturing processes. However, the advancement of technology has given rise to a new breed of robots known as collaborative robots, or cobots. These robots are revolutionising industries by working safely and efficiently alongside humans. What are Collaborative Robots? Unlike traditional ones confined to cages […]