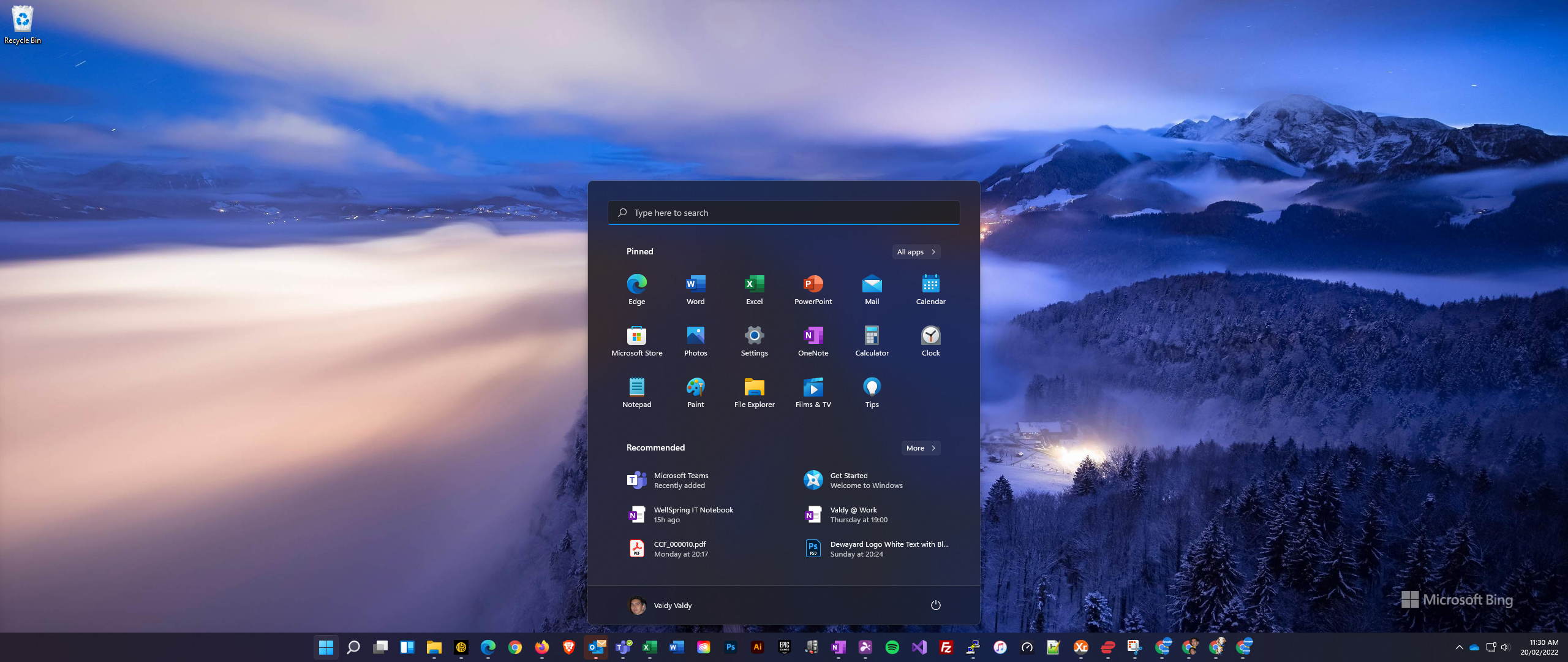
How to Download the Bill files in Telstra MBRS using Microsoft Edge
Background As Telstra MBRS portal is a legacy system and has no update for handling a modern browser and Internet Explorer has been decommissioning for a while now, it is a challenge to download the bill file using non-IE browsers. The issue is that when you click the download, a message pops up quickly and […]