Protect Your Business: Avoid These Cybersecurity Mistakes

Introduction
In today’s digital landscape, cybersecurity is crucial for business operations. As cyber-attacks and data breaches become more frequent, having a strong cybersecurity strategy is paramount. This blog will cover common cybersecurity mistakes made by businesses and provide practical tips to avoid them.
The rise of technology has led to a significant increase in cyber threats to businesses of all sizes. The cost can devastate small businesses that may not have the resources to recover from such an event.
Despite the growing awareness of cyber threats, businesses still make common cybersecurity mistakes that can leave them vulnerable to attacks. Here are some of the most prevalent mistakes:
Weak Passwords: Inadequate passwords provide hackers with a simple way to infiltrate confidential data. Therefore, businesses must promote the use of strong passwords and implement two-factor authentication where feasible, to reinforce security measures against cyber threats.
Lack of Employee Training: As stated earlier, human error plays a significant role in data breaches, and employees are often the weakest link in a company’s cybersecurity strategy. It’s important to provide regular training and education to employees to help them recognise and prevent common cyber threats, including phishing scams and social engineering attacks.
Outdated Software and Systems: Businesses that use outdated software and systems are at risk of cyber threats since they no longer receive security patches and updates. It is crucial for companies to regularly check for updates and security patches and apply them immediately to protect their systems from cyber threats.
“The average cost of a data breach in 2020 was $3.86 million.”
— Cost of a Data Breach Report 2020, Ponemon Institute
Insufficient Data Backup and Recovery Plans: Data loss can be catastrophic for a business. Companies should have a comprehensive data backup and recovery plan to ensure that critical data can be restored during a data breach or cyber-attack.
Lack of Firewall Protection: Firewalls are the first defence against cyber threats by blocking unauthorised access to a company’s network. Companies should ensure that all their systems and devices have a firewall to protect against potential attacks.
Failure to Monitor and Analyse Network Activity: Failing to monitor network activity can make detecting and responding to cyber threats difficult. Companies should invest in network monitoring tools to detect unusual activity and provide alerts to help mitigate potential threats.
Overreliance on Antivirus Software: While antivirus software is essential to a company’s cybersecurity strategy, it’s not enough on its own. Companies should implement a multi-layered security approach that includes firewalls, intrusion detection systems, and other tools to provide comprehensive protection against cyber threats.
Lack of Incident Response Plan: Even with the best cybersecurity strategies, it’s impossible to prevent all cyber-attacks. Companies should have an incident response plan in place to ensure a prompt and effective response to any cyber threats that may occur.
Lack of Employee Training
As businesses increasingly rely on technology, employees must receive cybersecurity training to prevent attacks. Unfortunately, many companies overlook the importance of training their employees, leaving them vulnerable to cyber-attacks.

Employee mistakes account for a significant percentage of data breaches. According to a study by the Ponemon Institute, human error is the cause of 95% of cybersecurity breaches. This demonstrates the importance of adequately training employees to prevent these incidents.
Weak passwords, clicking on suspicious links or attachments in emails, and falling for phishing scams are among the most common employee errors that result in cybersecurity breaches. Furthermore, in some cases, employees may unintentionally or purposefully expose sensitive information or fail to enforce essential security procedures.
Effective employee training is essential to prevent these types of incidents. Here are some tips for improving employee cybersecurity training:
Make training a regular part of the onboarding process: New employees should be trained on cybersecurity policies and best practices as part of their onboarding process. This ensures they start employment with the knowledge necessary to keep company data safe.
Use real-life scenarios: Employees are more likely to understand the importance of cybersecurity when presented with real-life scenarios. For example, use examples of recent data breaches to demonstrate the risks and the impact on the company.
“An average of 280 days to identify and contain a data breach, costing companies an average of $3.86 million.”
— Cost of a Data Breach Report 2020, IBM
Provide ongoing training: Regular training is crucial to keep employees up-to-date with the latest cybersecurity threats and best practices as cyber threats constantly evolve.
Test employees regularly: Regular testing can help identify areas where employees may need additional training. Conduct mock phishing tests and other simulations to assess employee knowledge and identify areas for improvement.
By prioritising employee cybersecurity training, businesses can reduce the risk of data breaches caused by human error and protect sensitive information from cyber-attacks.
Weak Passwords
One of the most common cybersecurity mistakes businesses make is using weak passwords. Weak passwords can easily be cracked, allowing hackers to gain access to sensitive information.
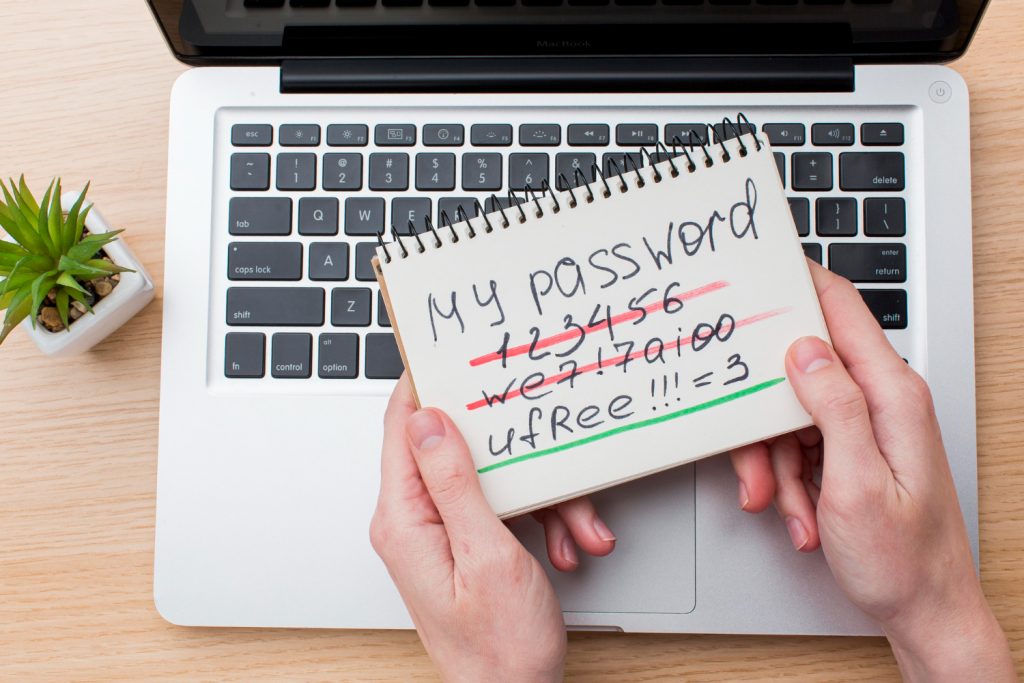
Here are some factors to consider when it comes to weak passwords:
Explanation of why weak passwords pose a cybersecurity threat
- Hackers can easily access sensitive information when weak passwords are used.
- Automated tools used by hackers can easily crack weak passwords, making them vulnerable targets.
- Weak passwords can also lead to other security vulnerabilities, such as phishing attacks.
Examples of common password mistakes made by employees and businesses
- Use simple passwords such as “password123” or “123456.”
- Reusing the same password for multiple accounts.
- Using personal information such as a name or date of birth as a password.
“81% of respondents had reused passwords across multiple accounts, putting their company’s security at risk.”
— The 2019 State of SMB Cybersecurity Report, Keeper Security
Tips for creating strong passwords and password policies
- Use upper and lowercase letters, numbers, and special characters.
- Avoid using personal information or common words in passwords.
- Use a password manager to securely store and manage passwords.
- Implement a password policy that requires regular password changes and prohibits reusing old passwords.
- Use two-factor authentication to add an extra layer of security to password-protected accounts.
Neglecting Software Updates
Software updates often contain necessary security patches that fix vulnerabilities and protect against cyber threats. Neglecting these updates can leave businesses open to cyberattacks.
Here are some critical points to consider:
Explanation of the importance of software updates for cybersecurity:
- Software updates often include critical security patches that protect against known vulnerabilities and exploits.
- Hackers frequently focus on outdated software that has known vulnerabilities because it is simple to exploit.
- Neglecting software updates can leave a business open to serious security risks.

Examples of consequences of neglecting software updates:
- In 2017, the WannaCry ransomware attack exploited a vulnerability in outdated versions of Windows operating systems. This attack affected over 200,000 computers in 150 countries, causing widespread damage and costing businesses billions of dollars.
- The Equifax data breach in 2017 was caused by a vulnerability in a web application software that was not patched promptly. This breach affected 147 million customers and resulted in significant financial and reputational damage to the company.
Tips for ensuring software is always up to date:
- Regularly check for and install software updates, including security patches.
- Consider using automated software update tools to ensure the timely installation of updates.
- Develop and implement a software update policy outlining procedures for promptly identifying and installing updates. This policy should be communicated to all employees and strictly enforced.
Ignoring Mobile Device Security
In today’s business world, mobile devices such as smartphones, tablets, and laptops are essential for conducting work. However, these devices pose a significant cybersecurity threat if not adequately secured.
Mobile devices can be lost or stolen, leading to data breaches and other security risks. Additionally, many employees use personal mobile devices to access company data, which can lead to further security vulnerabilities.
Examples of mobile device-related security breaches are numerous. For instance, in 2018, a cybersecurity firm discovered that an Android malware strain named “Skygofree” had stolen data from Italian mobile devices for years. Similarly, in 2020, a mobile app used by employees of a French cybersecurity firm was found to be vulnerable to hacking due to a lack of encryption.
To ensure mobile device security, businesses should take several precautions. Firstly, employees should be trained to use strong passwords and to update them regularly. Second, all mobile devices should be equipped with security software, including antivirus and anti-malware protection. Third, businesses should implement policies to manage mobile devices, including rules for employee-owned devices and the use of mobile apps.
Overlooking Physical Security
In today’s digital age, it’s easy to focus solely on cyber threats and overlook the importance of physical security. However, physical security is just as crucial to protecting your business’s sensitive information and data from falling into the wrong hands.
Explanation of how physical security is related to cybersecurity:
Physical security is the first line of defence against cyber attacks. Hackers can easily bypass digital security measures if they can physically access a computer or a network. For instance, an attacker could steal a laptop or mobile device, infiltrate a network using an open Ethernet port, or access a server room through an unlocked door.
“Businesses fell victim to a ransomware attack every 14 seconds, and this is projected to increase to every 11 seconds in 2021.”
— Cybercrime Report 2020, Cybersecurity Ventures
Examples of physical security threats that can lead to cybersecurity breaches:
- Theft or loss of laptops, smartphones, and other mobile devices
- Unauthorised access to restricted areas or data centres
- Unsecured computer equipment and hardware, such as routers and switches
- Lack of access controls for sensitive areas and information
- Poorly designed or implemented security policies and procedures
Tips for improving physical security:
- Develop and implement a comprehensive physical security plan: This should include policies and procedures for access control, visitor management, equipment and hardware security, and incident response.
- Secure your premises: This includes ensuring that all doors and windows have proper locks, surveillance cameras are installed in critical areas, and fences or barriers are in place to prevent unauthorised access.
- Implement access controls: Use physical barriers such as biometric readers, smart cards, or key fobs to control access to sensitive areas.
- Educate employees: Train employees on the importance of physical security and their role in keeping the business safe from physical threats. This includes reporting suspicious behaviour, following security protocols, and adequately securing equipment and hardware.
- Regularly review and update physical security measures: This should include periodic assessments of vulnerabilities, updates to policies and procedures, and testing of physical security controls.
By neglecting physical security, businesses leave themselves vulnerable to cyber attacks. Implementing these tips can help improve your business’s overall security posture, protecting your assets and ensuring your data’s confidentiality, integrity, and availability.
Ignoring Mobile Device Security
In today’s digital world, mobile devices such as smartphones and tablets are ubiquitous in our personal and professional lives. While they offer convenience and flexibility, they pose a significant cybersecurity threat if not properly secured. Here are some of the reasons why mobile device security is vital for businesses:
- Mobile devices are easily lost or stolen: Unlike desktop computers or servers, mobile devices are often carried around outside the office and can be easily lost or stolen. This can result in the exposure of sensitive company data to unauthorised individuals.
- Mobile devices can be infected with the malware: Malicious software, or malware, can be downloaded onto a mobile device through apps, email attachments, or other means. Once installed, the malware can compromise the security of the device and potentially steal sensitive information.
- Mobile devices can be used as a gateway to the company network: If a mobile device is compromised, it can provide a point of entry into the company network. This can allow cybercriminals to gain access to sensitive data or launch attacks on other devices on the network.
Examples of Mobile Device-Related Security Breaches
The risks associated with mobile device security are not just theoretical – numerous high-profile security breaches have resulted from mobile device vulnerabilities. Here are a few examples:
- The 2014 iCloud celebrity photo leak: Using a vulnerability in Apple’s “Find My iPhone” feature, hackers were able to repeatedly guess passwords for targeted accounts, eventually gaining access to the iCloud accounts of several celebrities and leaking their private photos and videos.
- The 2018 MyFitnessPal data breach: The personal information of 150 million users was compromised in a data breach of the mobile app MyFitnessPal. The data breach was caused by a vulnerability in the software of the app, which allowed hackers to obtain access to user data.
- The 2020 Twitter hack: Cybercriminals accessed the Twitter accounts of high-profile individuals such as Elon Musk and Barack Obama and used them to promote a cryptocurrency scam. Social engineering tactics made the attack possible by convincing Twitter employees to give the attackers access to the company’s internal systems.
“22% of data breaches were caused by errors, such as misconfigured databases or accidental disclosures.”
— 2020 Data Breach Investigations Report, Verizon
Tips for Securing Mobile Devices
To protect against mobile device-related cybersecurity threats, businesses should implement the following best practices:
- Use strong passwords: One way to ensure password security is to create passwords that consist of at least eight characters and contain a mix of uppercase and lowercase letters, numbers, and special characters. It is also important to change passwords frequently and avoid using the same password for multiple accounts.
- Install security software: Antivirus and anti-malware software should be installed on all mobile devices to detect and remove malicious software.
- Use encryption: Sensitive data stored on mobile devices should be encrypted to prevent unauthorised access in case the device is lost or stolen.
- Implement a mobile device management (MDM) system: An MDM system can allow businesses to remotely manage and secure mobile devices, enforce security policies, and wipe data from lost or stolen devices.
By following these tips, businesses can help ensure the security of their mobile devices and protect against cyber threats.
Using Outdated Technology
Outdated technology can pose a significant threat to a company’s cybersecurity. Using obsolete hardware and software can create security gaps that hackers can exploit. These security gaps allow attackers to access sensitive information or disrupt business operations.
Examples of Outdated Technology-related security breaches:
- Equifax data breach – The Equifax data breach in 2017 compromised the personal information of over 147 million customers, including social security numbers, addresses, and credit card numbers. The breach was attributed to an unpatched vulnerability in an outdated version of Apache Struts.
- WannaCry ransomware attack – The WannaCry ransomware attack, which occurred in 2017, targeted over 200,000 computers across 150 countries. The attack was possible due to a security flaw in older versions of Microsoft Windows operating systems that had not been updated with the necessary patches.
Tips for upgrading technology to improve cybersecurity:
- Regularly update software and firmware – Software and firmware updates often contain security patches that address known vulnerabilities. Regularly updating hardware and software can help ensure security gaps are quickly patched.
- Replace outdated hardware and software – If the vendor no longer supports hardware or software, it may be time to replace it with more up-to-date technology. This can help ensure that security gaps are addressed, and the latest security features are in place.
- Consider using cloud-based solutions – Cloud-based solutions provide a more secure and up-to-date technology environment. Cloud providers often have robust security features and regularly update their software and hardware to address security threats.
Lack of Cybersecurity Incident Response Plan
An effective cybersecurity incident response plan is an essential element of any business’s overall cybersecurity strategy. This plan provides clear guidelines and procedures for responding to potential cyber threats or incidents, such as a data breach or a malware attack.
With a solid incident response plan in place, businesses avoid not only suffering serious financial and reputational damage but also struggling to contain the breach or minimise the impact on their operations and customers.
Examples of cybersecurity incidents that require an incident response plan include:
- Ransomware attacks: A business may fall victim to ransomware, which is a type of malware that encrypts files and demands payment for the decryption key. By having a robust incident response plan in place, businesses can swiftly isolate and contain the ransomware, recover the encrypted data from backups, and reduce the impact of the attack.
- Phishing attacks: Phishing is a social engineering technique that aims to trick individuals into divulging sensitive information, such as login credentials or financial data. An incident response plan can help businesses quickly identify and respond to phishing attacks by informing employees of the attack and resetting compromised credentials.
- Data breaches: An occurrence where sensitive information, like customer data, is exposed or stolen is known as a data breach. A well-structured incident response plan can assist businesses in promptly identifying the source of the breach, evaluating the extent of the damage, and informing the affected parties.
To create an effective incident response plan, businesses should follow these tips:
- Establish a transparent chain of command: Define the roles and responsibilities of each team member involved in the incident response process, from IT professionals to legal and PR representatives.
- Test the plan regularly: Practice makes perfect, so test the incident response plan regularly through tabletop exercises or simulations.
- Ensure communication channels are in place: Establish communication channels, such as a dedicated incident response email address or phone number, to ensure everyone involved can communicate effectively and promptly.
- Keep the plan current: Cybersecurity threats and technology are constantly evolving, so updating the incident response plan regularly ensures it remains effective.
In conclusion, a lack of a cybersecurity incident response plan can leave businesses vulnerable to cybersecurity threats and can result in significant financial and reputational damage. By creating an effective incident response plan and regularly testing and updating it, businesses can be better prepared to respond to cybersecurity incidents and minimise their impact.
Conclusion
Cybersecurity is an essential aspect of modern business operations. Neglecting it can lead to disastrous consequences such as data breaches, financial losses, and reputation damage. This blog has explored some of the common cybersecurity mistakes businesses make and how to avoid them.
Businesses must invest in employee cybersecurity training to educate their staff on the best practices for preventing cyber attacks. Weak passwords are a significant cybersecurity threat, and businesses must ensure that they use strong passwords and implement robust password policies. Neglecting software updates can leave vulnerabilities that hackers can exploit. Therefore, businesses must prioritise software updates to protect against cyber attacks.
Mobile devices are ubiquitous in today’s business world and pose a significant cybersecurity threat. Businesses must secure their mobile devices and implement robust security measures to prevent mobile device-related breaches. Physical security is also essential for cybersecurity; companies must implement measures to ensure their physical assets.
Outdated technology is also a significant cybersecurity threat. Businesses must prioritise technology upgrades to use the latest security features and protocols. Finally, a cybersecurity incident response plan is crucial for responding quickly and effectively to cyber attacks. Businesses must develop and test an incident response plan regularly to ensure effectiveness.
In summary, businesses must take cybersecurity seriously and prioritise it to avoid the costly consequences of cyber attacks. By implementing the tips outlined in this blog, businesses can protect themselves against cyber threats and ensure their continued success.
Be sure to check out our other related posts if you enjoyed this one:
- The Rise of Collaborative Robots: Transforming Industries
- Unmasking Cyber Secrets: The Art of Deception Revealed!
- Decoding Cyber Threats: The Social Engineering Menace
- Unlock the Ultimate Quest: Ready Player One’s Audio Adventure!
- Revolutionising Wellness: Metaverse Therapy Unleashes Mental Liberation!
- Code Mastery Unleashed: Transform Your Skills with Clean Code by Robert C. Martin! 🚀
- Top Must-Have Tech Gadgets for Kids – Unbelievable Fun!
- Mastering Crypto Trading: Proven Strategies
- Unveiling Ethereum 2.0: Advancements & Impact
- AI Transforms E-Commerce: A Digital Revolution
Sign up for updates on this blog and our latest tech posts if you enjoyed reading this one.
Credits
- Featured image by RawPixel.com on Freepik.
- Lack of employee training image by KateMangoStar on Freepik.
- Weak password image by Freepik.
- Neglecting software updates photo by ThisIsEngineering on Pexels.









